DATASERV SECURITY 360
Multi-Layered Security for your Business
The cost to adopt a layered security solution is far less expensive than the cost to recover from breaches and compromised or corrupt data.
To Protect your business, we subscribe to the multi-layer approach.
-plans may differ on protection and features.
Next-Gen Firewall with an applied Security Subscription
Email spam filtering
Email backup of critical email boxes
DNS URL Filtering - Cloud Based
Superior Threat Management with SOC and MDR
Controlled Patch Management for desktops and server
Active Directory Group Security Policies for securing internal network folders
2-Factor Authentication Implemented Throughout the Business
User Phish Email Training
Data Backup on and off-site 3-2-1 rule applied for fail-safe protection of your data
The cost to adopt a layered security solution is far less expensive than the cost to recover from breaches and compromised or corrupt data.
MANAGED FIREWALL
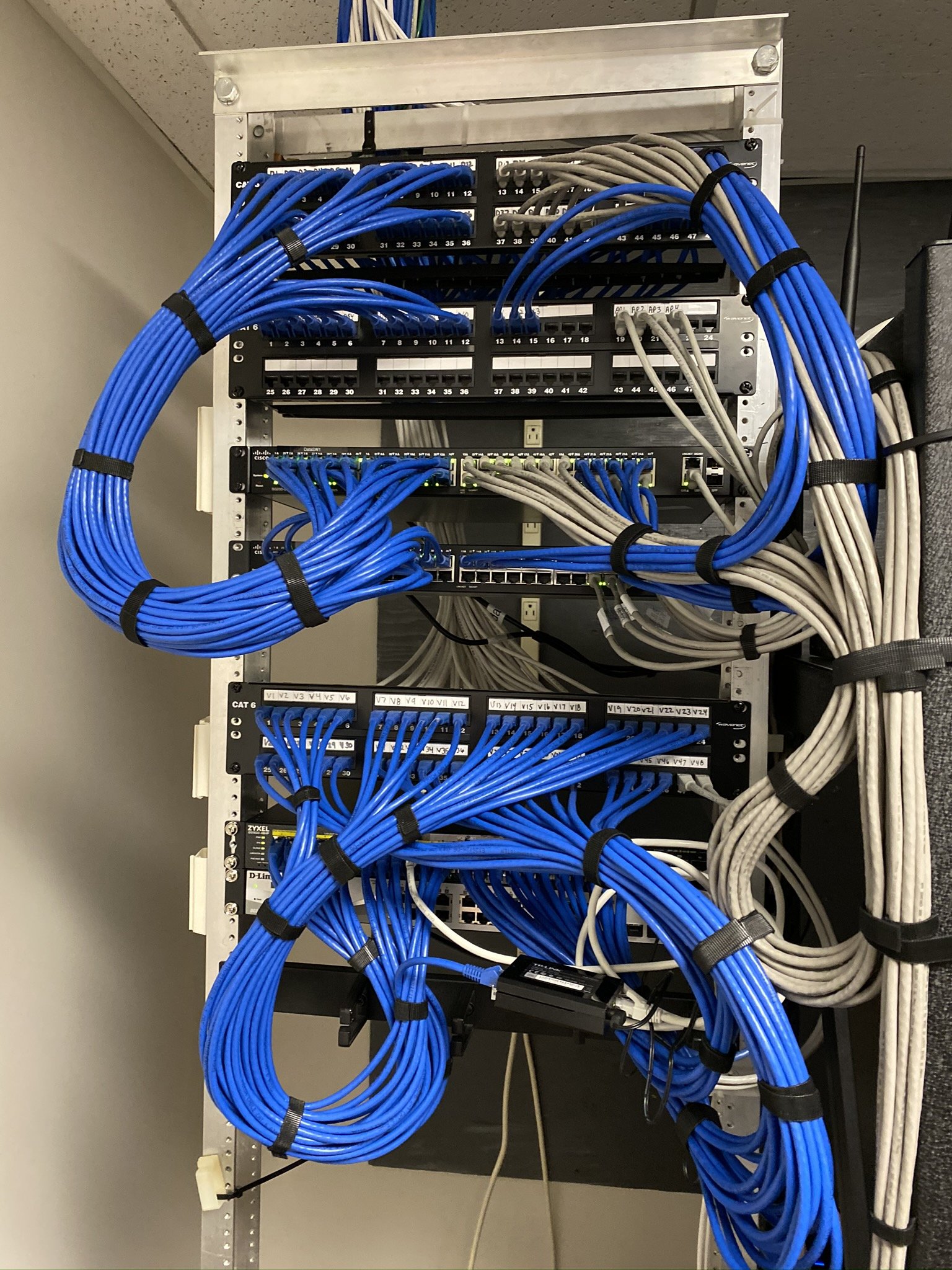
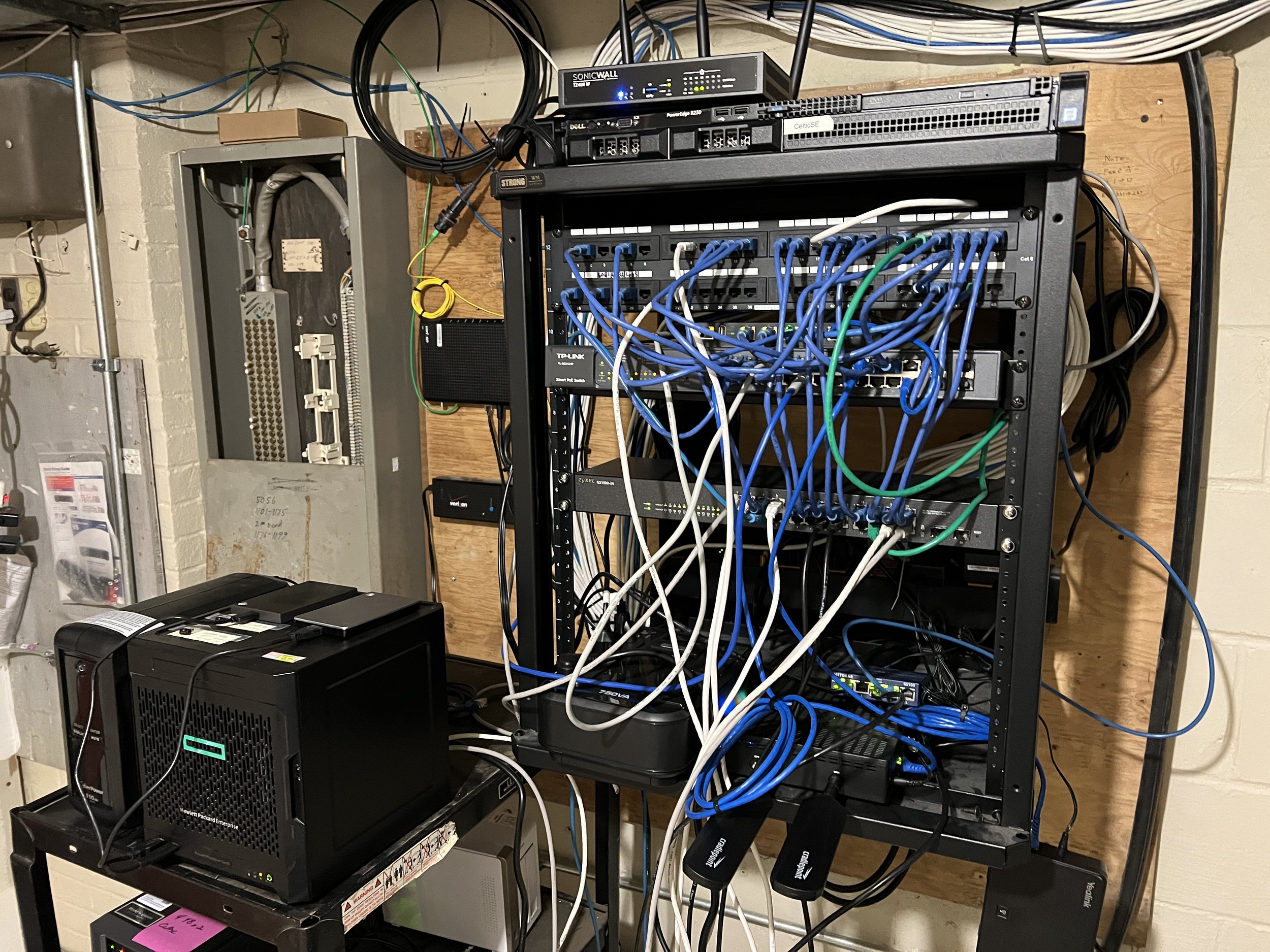
This starts with a managed firewall professionally configured based on your network needs with a current security subscription to protect your network against point of entry viruses, malware, botnets, productivity robbing content.
Managed Wi-Fi would also come under this security feature. Recommended implementation of a public Wi-Fi network for all non-essential devices not needing internal network access. This secures your network against rogue cell phones, tablets, guest laptops and Io T devices.
EMAIL SECURITY
Email Layer Security starts with a battle-tested cloud-based spam filtering service. Dataserv provides the most sophisticated and most comprehensive real-time protection from email phishing threats through our Phishing Firewall, External Sender flagging, real-time databases of safe and dangerous sites, and flexible phishing content handling policies.
This enables us to provide end-to-end protection from phishing on any device or service that receives email, without requiring installation and configuration of any software, and our phishing policies can help you customize the level of protection your users get.
According to a recent study by Verizon (2019), over 90% of security compromises start with a spear-phishing email. We can eliminate spear-phishing threats or just provide notifications to your users when they get tricked into clicking on a link leading somewhere dangerous.
EMAIL BACKUP
The control and protection required for your Office 365 data
Protecting on-premises data is a no-brainer. But many organizations overlook protecting cloud data because they believe this is covered as part of their cloud service.
Microsoft provides powerful services within Office 365 – but a comprehensive backup of your Office 365 data is not one of them.
Dataserv Backup for Microsoft Office 365 eliminates the risk of losing access and control over your Office 365 data including Exchange Online, SharePoint Online OneDrive for Business, and Microsoft Teams – so that your data is always protected and accessible.
Why backup Office 365?
Microsoft Office 365 enables your enterprise to work anywhere, anytime, without the need to host your own email, files, and SharePoint infrastructure. Even though Microsoft hosts the infrastructure, this doesn’t replace your responsibility of maintaining a backup of your business-critical Office 365 data.
With Office 365, it's your data — you control it — and it is your responsibility to protect it.
Dataserv Backup for Microsoft Office 365 gives you the power to securely backup Office 365 and:
Protect your Office 365 data from accidental deletion, security threats, and retention policy gaps
Quickly restore individual Office 365 email, files, and sites with industry-leading recovery flexibility
Meet legal and compliance requirements with efficient eDiscovery of Office 365 items
NETWORK, SERVER, and DESKTOP THREAT MANAGEMENT
Dataserv offers the best multi-layered desktop protection against malware, ransomware, exploits, and fileless attacks in a lightweight client that will not bog down system resources.
Converges XDR, Response, Automation, and 24/7 MDR Services, Dataserv utilizes the World’s First Autonomous Breach Protection Platform
INCLUDED 24/7 MDR (Managed Detection & Response) SERVICES
Proactive Threat Hunting
Decoy files, machines, user accounts, and network connections to lure and detect advanced attackers
Preset behavior rules coupled with dynamic behavior profiling to detect malicious anomalies
Ask Dataserv for a demo of this awesome product.
CONTROLLED PATCH MANAGEMENT
Cyber attackers typically search for the easiest way to breach a network. Often, this involves pinpointing “soft targets,” such as software that has not yet been updated to protect against known malware. It is critical your device is updated with the latest security patches.
Patch Management solution handles every facet of patching on business desktops. It discovers relevant and essential service packs, security updates, and other hotfixes, and then installs them on the appropriate machines.
Automating these tasks ensures that customer hardware and software stay up to date while eliminating the need for you to perform these tasks manually.
GROUP POLICY SECURITY
Group Policy Security requires a windows server or cloud-based active directory service. There are some simple group policy settings, which if appropriately configured, can make your network far safer than without them. You can make your organizational network safer by configuring the security and operational behavior of computers through group policy. Through group policy, you can prevent users from accessing specific resources, run scripts, and perform simple tasks such as forcing a particular home page to open for every user in the network.
TWO FACTOR AUTHENTICATION
Two-factor authentication (2FA), sometimes referred to as two-step verification or dual-factor authentication, is a security process in which the user provides two different authentication factors to verify themselves to better protect both the user's credentials and the resources the user can access. Two-factor authentication provides a higher level of assurance than authentication methods that depend on single-factor authentication (SFA), in which the user provides only one factor -- typically a password or passcode. Two-factor authentication methods rely on users providing a password as well as a second factor, usually either a security token or a biometric factor like a fingerprint or facial scan. You can also download an authentication app on your phone for access to 2FA Enabled sites.
Two-factor authentication adds an additional layer of security to the authentication process by making it harder for attackers to gain access to a person's devices or online accounts because knowing the victim's password alone is not enough to pass the authentication check. Two-factor authentication has long been used to control access to sensitive systems and data, and online service providers are increasingly using 2FA to protect their users' credentials from being used by hackers who have stolen a password database or used phishing campaigns to obtain user passwords.
EMAIL PHISHING TRAINING
Reduce your largest attack surface — your end-users
Phishing is big business. Attacks have shown record growth in recent years, and a solid security awareness program is an integral part of any defense-in-depth strategy. Sophos Phish Threat educates and tests your end users through automated attack simulations, quality security awareness training, and actionable reporting metrics.
Phish Threat provides you with the flexibility and customization that your organization needs to facilitate a positive security awareness culture.
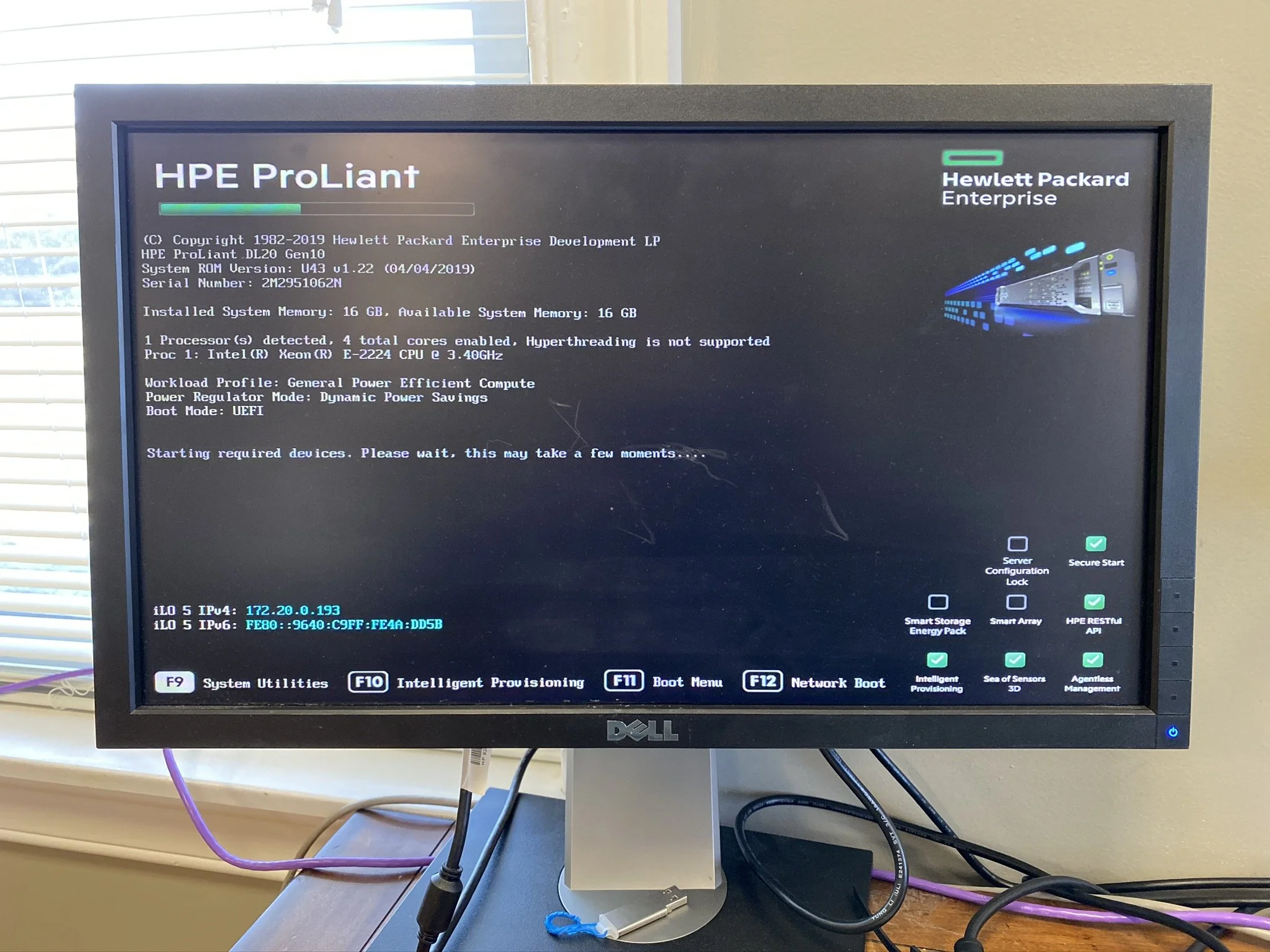
CloudSecure DATA BACKUP Hipaa compliant, 256bit encrypted
If you’re looking into backup and recovery solutions, you’re going to hear the phrase “3-2-1 backup” come up a lot. You’ll hear it from most IT consultants and IT pros as well as many backup vendors, who will speak about their products in terms of 3-2-1 compliance.
The 3-2-1 rule is the best practice for backup and recovery. It means that when you build out your backup and recovery strategy you should:
1. Keep at least three copies of your data
That includes the original copy and at least two backups.
2. Keep the backed-up data on two different storage types
The chances of having two failures of the same storage type are much better than for two completely different types of storage. Therefore, if you have data stored on an internal hard drive, make sure you have a secondary storage type, such as external or removable storage, or the cloud.
3. We keep at least one copy of your data offsite with multiple revisions. We encrypt your data with 256bit encryption in transit and at rest in the data center for full privacy.
Even if you have two copies on two separate storage types but both are stored onsite, a local disaster could wipe out both. Keeping a third copy in an offsite location secures your data from lightning, fire, or theft, or act of God.
The 3-2-1 backup rule is a best practice because it ensures that you’ll have a copy of your data no matter what happens. Multiple copies prevent you from losing the only copy of your data. Multiple locations ensure that there is no single point of failure and that your data is safe from disasters such as fires and floods.
We recommend whenever speaking to a backup vendor to make sure that you ask them how their backup solution fits with 3-2-1 compliance.
Ready to get started with a 3-2-1- compliant solution? Sign up for a free, no-risk 30 day trial of CloudSecure Server and start protecting your data today.
And that's our current list of protective layers for your business. Feel free to call us for a more in-depth conversation on any or all of the above subjects.